

Share on social..
By Richard McBarnet, Managing Director, Lumina Technologies
If your engineers are still walking USB sticks from the design office to the shop floor to load jobs onto your CNC machines, you already know the problems it creates.
It works. But it’s not secure, it’s not efficient, and if you’re working toward Cyber Essentials certification, it’s creating risks you’ll need to address.
There’s a better way.
 Most people don’t realise that the operating system inside a CNC machine isn’t a standard version of Windows. It’s an embedded version — separately licensed, built specifically for machines with computing cards and processing power. But if you log into one, it looks like a Windows PC. And that’s when people get a surprise.
Most people don’t realise that the operating system inside a CNC machine isn’t a standard version of Windows. It’s an embedded version — separately licensed, built specifically for machines with computing cards and processing power. But if you log into one, it looks like a Windows PC. And that’s when people get a surprise.
We’ve seen machines running Windows 7, Windows XP, even Windows NT4 — which takes us back to the late 1990s.

If you bought a new CNC milling machine today, it would probably come with Windows 10 or Windows 11 embedded. But Windows 10 is already end-of-life from a PC perspective, and even for embedded systems, vendor-supported updates only last so long. Eventually the vendor stops issuing updates and the machine carries on working with whatever system it has.
And just as with PCs, you can’t shoehorn a modern operating system onto older hardware. Windows 11 is very specific about the processor, the TPM chip, and the memory requirements. Upgrading these machines to a modern operating system is simply a non-starter. It can’t happen.
But equally, businesses aren’t going to throw these machines out. They still have all the technical capability to deliver the function they were designed for. So, we have to find an alternative solution.
 The first thing most businesses think of is air gapping — just unplug the machine from the network entirely. If it’s not connected, it can’t be compromised, and from a Cyber Essentials perspective it’s effectively taken out of scope.
The first thing most businesses think of is air gapping — just unplug the machine from the network entirely. If it’s not connected, it can’t be compromised, and from a Cyber Essentials perspective it’s effectively taken out of scope.
That’s true, up to a point. An air gap does provide a clear, non-bridgeable boundary between the internet and the machine. It absolutely solves the cyber exposure problem.
But the consequence is that your engineers now need to use some form of transportable media to transfer work onto the machines. In practice, that means USB sticks, maybe a USB hard drive. And because of the age of these machines and their inability to deal with encrypted drives, they’ll be using unencrypted devices. A fresh USB stick straight out of the packet, loaded with the job from the design office, then carried over to the machine on the shop floor.

The inherent risk is obvious. Any time you have an unencrypted device that’s physical and portable, you run the risk of it being lost, mislaid, put in a pocket and forgotten about, taken home. You have no control over the data. You’re not creating any security boundary around it.
So, the air gap solves the internet problem but creates a data security problem. You’ve moved the risk from A to B.

The logical next step is to encrypt the USB drives. But for most legacy CNC machines, that’s a non-starter too. The machines are too old to decrypt or open the encryption at the other end. So, you’re stuck — air gapping forces you into USB sticks, and the USB sticks can’t be made secure because the machines can’t handle encryption.
We still need a better solution.
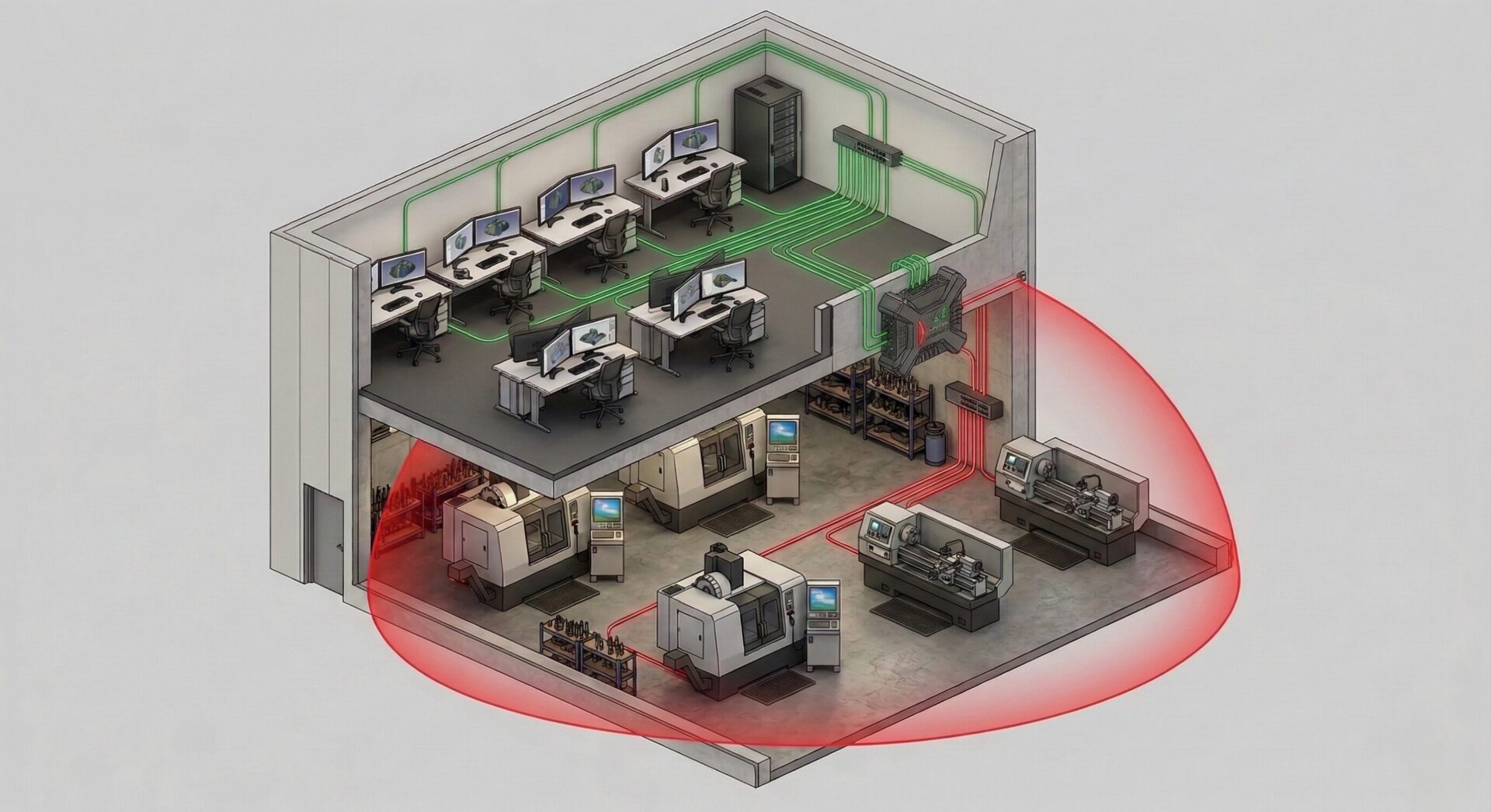
The best solution — and the one that effectively ticks every box — is a segregated network.
What we do is create a separate network, or VLAN (a virtual local area network), and isolate it from the internet. There’s absolutely no internet connectivity to or from that VLAN. It’s the virtual equivalent of the air gap we had before.

But because it’s electronic and we can manipulate it, we can create controlled routes from that segregated network to the workstation network or server network — wherever the design files are stored. Those routes only exist between those two zones. So a workstation in the design office can access both the internet and the segregated machine network — but through completely separate routes. The internet connection never reaches the isolated machines. They’re connected to your internal network, but sealed off from everything else.
By managing that segregated network separately, managing all the security boundaries around it, and using access control lists to determine who can access it, we create the equivalent of an air gap without pushing engineers to use USB sticks — which just creates a secondary problem.
The machines receive their G-code and design files electronically, directly from the design office. No USB sticks. No unencrypted data walking out the door. No version control headaches. The problem is solved completely.
 From a Cyber Essentials perspective, these machines are taken out of scope — which the certification framework allows for legacy hardware with operating systems that can’t be updated. But the key point is that you’ve achieved this without air gapping, without USB sticks, and without compromising how your engineers work.
From a Cyber Essentials perspective, these machines are taken out of scope — which the certification framework allows for legacy hardware with operating systems that can’t be updated. But the key point is that you’ve achieved this without air gapping, without USB sticks, and without compromising how your engineers work.
For anyone running legacy hardware or machines with legacy operating systems or firmware, segmenting the network your CNC machines are on, is the only sensible, viable route to go down.
– Richard McBarnet, IT Expert & Lumina CEO

If you’re running legacy CNC equipment, or your engineers are still using USB sticks to load jobs, or wondering whether Cyber Essentials is achievable for your business, we can help you find out. Contact us via the contact form on the side, or call 01442 500 890 for a free IT review of your legacy machinery.